On February 23, 2026, the Ransomware-ISAC community was alerted by Tammy Harper to a new malware threat, VEN0m, which leverages User Access Control (UAC) bypass and Bring Your Own Vulnerable Driver (BYOVD) tactics. Following the alert, the team conducted an analysis of the open-source Rust-based ransomware designed to disrupt antivirus installations and compromise endpoint security.
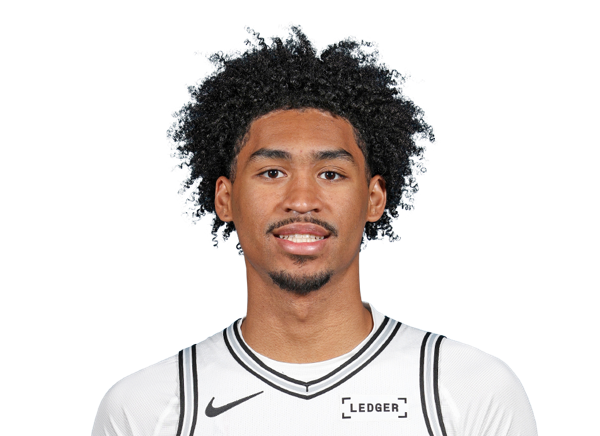
"We detonated VEN0m against two different endpoint security settings," said Eric Taylor, one of the authors of the detailed analysis. The ransomware executed its rigorous attack chain, which includes nine phases such as kernel driver loading, file encryption using AES-256-GCM, and ransom note delivery, all without detection on the Windows Defender system.
"We detonated VEN0m against two different endpoint security settings,"
The first phase of the attack showcased a concerning effectiveness by entirely evading detection on a fully-patched Windows 11 Pro system running Windows Defender. Nevertheless, against a commercial EDR solution equipped with vulnerable driver protection, the intrusion was thwarted a mere 127 milliseconds after launch.
"The attack chain collapsed immediately due to a single behavioral detection which flagged a vulnerable driver located in a user-writable directory," Taylor remarked, illustrating the rapid countermeasures that can disrupt ransomware attacks.
"The attack chain collapsed immediately due to a single behavioral detection which flagged a vulnerable driver located in a user-writable directory,"

This comprehensive report outlines both the unimpeded and halted executions of VEN0m, providing insights into the malware’s design and functionality. Among the key findings, the analysis reveals how the encryption key for the payload is recoverable in an uncomplicated manner. "The AES-256 key is a hardcoded plaintext ASCII string found in the PE`.rdata` section, retrievable from the persistence binary using simple tools in less than a minute," pointed out Tammy Harper, emphasizing the flaws in the ransomware’s security measures.
Looking Ahead
Looking Ahead
Looking Ahead
The report further includes a complete Incident Response (IR) playbook which encompasses containment, key recovery, eradication, and hardening procedures, aimed at educating security teams on responding to future attacks. With 42 behavioral detection queries crafted over the nine phases of the attack, the findings are intended not just for the specific VEN0m strain but also for other ransomware variants employing similar BYOVD tactics.
"Our analysis provides a wealth of data — over 8,500 SIEM events along with over 50,000 Sysmon events were analyzed across different detonations, allowing for a comprehensive reconstruction of the attack timeline and development of behavior-based detection strategies," explained Taylor.
"Our analysis provides a wealth of data — over 8,500 SIEM events along with over 50,000 Sysmon events were analyzed across different detonations, allowing for a comprehensive reconstruction of the attack timeline and development of behavior-based detection strategies,"
Security teams, including SOC and Incident Response professionals, are urged to consult various sections of the report corresponding to their expertise. Specifically, they should focus on developing detection strategies and understanding the attack chain in-depth. For managers and executives, essential highlights are listed in the executive summary, while security researchers are motivated to delve into the code-level analysis provided within the report.
The analysis also provides insights into the open-source aspects of the ransomware's development, showcasing how CVE-2025-26125 exploits existing vulnerabilities to form a weaponized ransomware payload.
Looking Ahead
Looking Ahead
As organizations continue to adapt their defenses against sophisticated ransomware attacks, findings such as those highlighted in this report on VEN0m serve as crucial tools in understanding how to bolster cybersecurity strategies. With malware evolving rapidly, maintaining an updated awareness of detection methods and recovery processes remains imperative to thwart future incursions.



