A newly identified ransomware family known as Midnight has emerged on the cybersecurity scene, disrupting traditional ransom models by incorporating a critical flaw that allows victims to recover their encrypted files without having to pay. This development has drawn the attention of cybersecurity experts, particularly due to Midnight's ties to the notorious Babuk ransomware framework.
Researchers at Gen Digital noted, "A new ransomware strain known as Midnight has emerged, echoing the notorious tactics of its predecessor, Babuk. Midnight blends familiar ransomware mechanics with novel cryptographic modifications – some of which unintentionally open the door to file recovery." This revelation has significant implications for both victims and the ongoing battle against ransomware attacks.
Midnight is considered a descendant of Babuk, a ransomware-as-a-service (RaaS) operation that surfaced in 2021 before its code was leaked. This leak paved the way for a host of derivative strains, including notable examples like ESXiArgs and Rorschach.

The researchers elaborated, "In mid-2021, Babuk’s operators abruptly shut down and leaked their full source code, including builders for Windows, ESXi, and NAS variants. This leak led to a wave of inspired ransomware families, each modifying Babuk’s original design to suit their own goals. Midnight is one such evolution."
Although Midnight maintains many of the elements that made Babuk effective, it introduces notable changes. Instead of employing Babuk's HC-256 algorithm, Midnight adopts ChaCha20 for file encryption, coupled with RSA for key wrapping. However, this modification has inadvertently led to a vulnerability in their encryption process.

When encrypting files, Midnight appends the extensions “.Midnight” or “.endpoint.” Interestingly, in certain builds, there are no changes made to file names; instead, the ransomware appends the extension to the end of the file content. This characteristic can be confirmed through hex editing tools.
Victims are typically met with a ransom note titled How To Restore Your Files.txt, which varies slightly based on whether files were encrypted with the .Midnight or .endpoint variants. This tactic is a common strategy among ransomware operatives to establish communication with their victims.
Additionally, security researchers have identified a mutex named Mutexisfunnylocal within the ransomware code, which serves the purpose of preventing multiple instances of Midnight from executing simultaneously. Some builds may also leave behind logs, such as Report.Midnight or debug.endpoint, that can facilitate recovery efforts.
Midnight offers multiple command-line arguments that can customize its operation. These include targeting specific directories and enabling encryption on network drives, displaying the sophistication of its operation.
Career Journey
Career Journey
Career Journey
Historically, Midnight's attackers showed a preference for high-value files, targeting databases and backup files. Still, recent iterations of the ransomware broadened its scope, now encrypting nearly all file types while leaving certain executable files untouched.
The encryption mechanics stand at the core of the ransomware's flawed effectiveness. Gen analysts observed, “Midnight uses ChaCha20 for encrypting file contents and RSA for encrypting the ChaCha20 key. The RSA-encrypted key, along with its SHA256 hash, is appended to the end of each encrypted file. This format is consistent across known samples.”
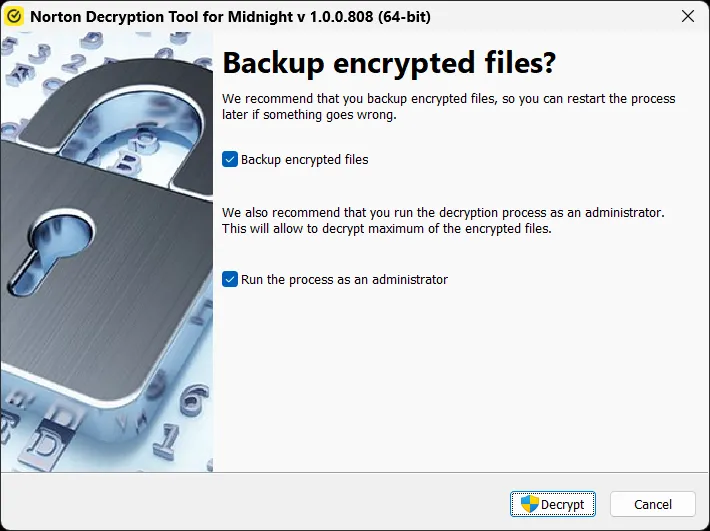
Due to errors in the implementation of key handling and data padding, researchers at Gen were able to devise a functional decryptor that circumvents the need for the attackers’ private key entirely. This loophole presents a unique opportunity for victims, enabling them to recover their lost files at no charge via a tool known as the Norton Midnight Decryptor.
Detailed guidelines along with the decryptor's links for both 64-bit and 32-bit Windows systems have been made publicly available: norton_decryptor_midnight.exe and norton_decryptor_midnight64.exe. This allows victims to exploit the weak RSA implementation and restore the ChaCha20 keys initially utilized in the encryption process.
Overall, the emergence of Midnight underscores the ongoing arms race in cybersecurity, where new threats continually adapt and evolve. However, the discovery of exploitable vulnerabilities offers a flicker of hope for those affected, turning what is often a nightmare scenario into an opportunity for reclaiming personal data without financial sacrifice.