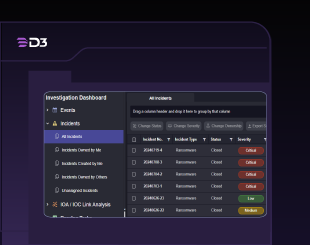
In an era where cyberattacks are becoming increasingly sophisticated and frequent, Security Operations Centers (SOCs) are under immense pressure to respond quickly and effectively to threats. D3 Security has stepped into this challenging landscape with the launch of Smart SOAR, an innovative platform designed to transform how organizations handle incident response and management.
The cybersecurity industry has long grappled with the challenge of information overload, where security teams are bombarded with alerts and data that can obscure genuine threats. Smart SOAR addresses this critical pain point by converting what D3 Security describes as "overwhelming data noise" into manageable, high-fidelity incident records that enable security teams to respond with confidence.
"overwhelming data noise"
"Your incident responders have limited time, so they need tools that enable them to spend their precious time on real threats," explained a D3 Security representative, highlighting the core philosophy behind the new platform.
"Your incident responders have limited time, so they need tools that enable them to spend their precious time on real threats,"

Team Dynamics
At its foundation, Smart SOAR is built as an automated incident response solution specifically tailored for mature SOCs. The platform leverages automation to help teams improve their Mean Time to Resolution (MTTR) while ensuring they maintain complete control over incident management processes. This balance between automation and human oversight represents a significant evolution in how security operations can be conducted.
Team Dynamics
The power of Smart SOAR lies in its sophisticated automation capabilities. "Automation-powered workflows allow you to keep up with the fastest-moving incidents, providing the data you need to make key decisions and the orchestration needed to turn those decisions into action," the development team explained. This approach recognizes that modern cyber threats often move at machine speed, requiring equally rapid response capabilities.
"Automation-powered workflows allow you to keep up with the fastest-moving incidents, providing the data you need to make key decisions and the orchestration needed to turn those decisions into action,"
The platform operates on three distinct tiers of information, facilitating automated triage and enrichment at the event level. This structure creates an extensive library of automated utility commands, all managed through a risk-scored queue that can handle various alert sources. This systematic approach ensures that the most critical threats receive immediate attention while less urgent matters are appropriately prioritized.
Championship Implications
One of Smart SOAR's standout features is its focus on addressing critical use cases that security teams encounter daily. The platform comes equipped with incident-specific workflows designed to handle common but serious security scenarios. "Codify effective responses to your most important use cases. Smart SOAR has the incident-specific workflows to help you respond to phishing campaigns, infected endpoints, data breaches, and more," stated a company spokesperson.

The platform includes an out-of-the-box playbook library that is rooted in MITRE-based incident response methodologies, providing teams with proven frameworks for tackling common incidents efficiently. This is particularly valuable for handling large-scale phishing campaigns, where Smart SOAR can group related events and streamline the investigation process across multiple alerts, significantly reducing the time and resources required for comprehensive response.
Perhaps most innovatively, Smart SOAR introduces a behavior-based approach to threat response that goes beyond traditional methods. The platform incorporates playbooks that utilize MITRE ATT&CK's recommended mitigations and detection strategies for techniques identified in security incidents. "Use the MITRE D3FEND model for responding to adversary techniques and anticipate their next moves by mapping their techniques to the MITRE ATT&CK matrix," the D3 Security team advised.
"Use the MITRE D3FEND model for responding to adversary techniques and anticipate their next moves by mapping their techniques to the MITRE ATT&CK matrix,"
This behavioral approach represents a significant advancement over traditional Indicators of Compromise (IOCs), as it correlates events based on attacker behavior patterns rather than just specific signatures or indicators. This methodology enables security teams to better understand and predict adversary actions, potentially stopping attacks before they can cause significant damage.
The platform's comprehensive approach to incident resolution extends beyond quick fixes to address underlying security issues. Through powerful playbooks, investigation management tools, and evidence tracking capabilities, Smart SOAR enables teams to tackle the root causes of security incidents effectively.
Real-world implementation of the platform has already shown promising results. Steve Sampana, Security Operations Manager in the financial services sector, shared his positive experience: "With the help of D3, we managed to convert the overly complex playbooks of our security analysts. We didn't have to do escalations manually to a ticketing system; it did it all for us."
Smart SOAR's design philosophy centers on enabling SOC teams to focus on high-priority work without becoming overwhelmed by administrative tasks. By integrating seamlessly across the security stack, the platform offers a centralized queue for all security incidents, dramatically simplifying incident management processes.
"Leverage risk-based autonomous triage to get a full understanding of which incidents are the most urgent," explained the development team. This prioritization capability allows teams to allocate their resources more effectively and enhance overall productivity.
"Leverage risk-based autonomous triage to get a full understanding of which incidents are the most urgent,"
The platform also emphasizes collaboration through automated task assignment, notifications, comprehensive reporting, and streamlined communication tools. This interconnected approach fosters a more efficient methodology for tackling security incidents swiftly and comprehensively, potentially transforming how modern SOCs operate in an increasingly complex threat landscape.