In the realm of cybersecurity, the term 0day, pronounced "zero day," signifies a critical software vulnerability that remains undiscovered by the public and the software vendor. As these vulnerabilities appear, attackers can exploit them immediately, creating a significant risk because developers have no time—zero days—to implement a defense before breaches occur.
"zero day,"
"0day vulnerabilities are highly sought after by hackers, as they can leverage these flaws to gain unauthorized access to systems, steal sensitive data, or execute other malicious actions without detection," explained a cybersecurity expert. The urgency surrounding 0day vulnerabilities underscores their severity in the cybersecurity landscape.
"0day vulnerabilities are highly sought after by hackers, as they can leverage these flaws to gain unauthorized access to systems, steal sensitive data, or execute other malicious actions without detection,"
Once a 0day is identified, the typical response involves the notification of the software vendor responsible for the affected application, prompting them to develop a patch aimed at fixing the issue. However, this cyber cat-and-mouse game puts users in precarious positions until those patches are available and fully deployed.

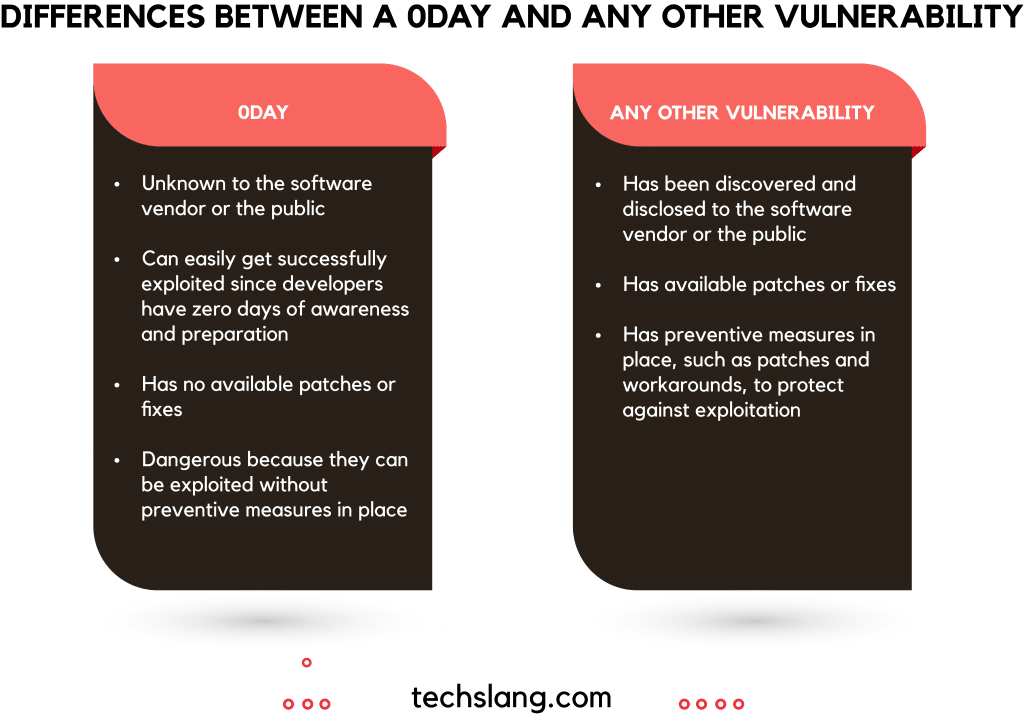
The distinction between a 0day vulnerability and more common security flaws lies in the level of awareness and the availability of patches. A 0day vulnerability is characterized by its obscurity, leaving both the vendor and users unaware of its existence. This lack of awareness means that when a hacker capitalizes on a 0day vulnerability, no preemptive measures or fixes exist. "Once a vulnerability is known, vendors can promptly work on fixes, but with 0day vulnerabilities, the timeline is non-existent before exploitation can begin," said a senior analyst at a cybersecurity firm.
"Once a vulnerability is known, vendors can promptly work on fixes, but with 0day vulnerabilities, the timeline is non-existent before exploitation can begin,"
Conversely, known vulnerabilities are regularly disclosed and documented, allowing users to implement safeguards more effectively. "Proactive measures such as applying patches or employing workarounds significantly reduce the risk associated with already identified vulnerabilities," stated a cybersecurity manager.
"Proactive measures such as applying patches or employing workarounds significantly reduce the risk associated with already identified vulnerabilities,"
Protecting systems against 0day vulnerabilities presents unique challenges, yet several strategies can help mitigate risk. Staying informed about cybersecurity threats is critical. "Keeping up with the latest security news and advisories from trusted sources can alert organizations to potential vulnerabilities," noted an information security officer.
"Keeping up with the latest security news and advisories from trusted sources can alert organizations to potential vulnerabilities,"
Defense-in-depth is another recommended strategy. This approach involves implementing multiple security layers to safeguard systems. "Combining tools like firewalls, intrusion detection systems, and antivirus software can effectively fortify defenses against potential attacks," explained a security consultant.
"Combining tools like firewalls, intrusion detection systems, and antivirus software can effectively fortify defenses against potential attacks,"

Network segmentation also adds an important layer of security by limiting the damage caused by any successful breach. "By separating sensitive systems from those that are less critical, organizations can prevent attackers from easily moving laterally within a network once they gain entry," said an IT security architect.
"By separating sensitive systems from those that are less critical, organizations can prevent attackers from easily moving laterally within a network once they gain entry,"
Application whitelisting further strengthens security protocols by restricting users to pre-approved applications. This method can serve as a deterrent against unauthorized software execution should a vulnerability be exploited. "It’s essential to ensure that only trusted applications can run within your environment," emphasized a network security specialist.
"It’s essential to ensure that only trusted applications can run within your environment,"
Additionally, user education plays a crucial role in defense against 0day exploits. "Training users to recognize suspicious behaviors, avoid clicking on questionable links, and maintain strong, unique passwords can vastly improve overall security posture," shared a cybersecurity trainer.
"Training users to recognize suspicious behaviors, avoid clicking on questionable links, and maintain strong, unique passwords can vastly improve overall security posture,"
While the challenge of defending against 0day vulnerabilities persists, ongoing vulnerability management remains necessary. "Continuously scanning and addressing known vulnerabilities provides a solid foundation for mitigating risk, even if it doesn’t address 0day threats specifically," noted a corporate security advisor.
"Continuously scanning and addressing known vulnerabilities provides a solid foundation for mitigating risk, even if it doesn’t address 0day threats specifically,"
Employing behavioral analysis tools can also provide insight into potentially compromised systems. "These tools help detect unusual activities within a network, flagging potential issues before they escalate into full-blown breaches," commented a cybersecurity researcher.
"These tools help detect unusual activities within a network, flagging potential issues before they escalate into full-blown breaches,"
Lastly, transitioning towards a zero-trust security model can significantly enhance protection strategies. "This approach operates on the principle that threats can come from both outside and inside the organization, requiring a thorough verification process for every request," explained a cybersecurity policy expert.
"This approach operates on the principle that threats can come from both outside and inside the organization, requiring a thorough verification process for every request,"
In conclusion, being proactive about cybersecurity measures is vital to mitigating the risks posed by 0day vulnerabilities. As the once-hidden threats become increasingly recognized, stakeholders must prioritize not only awareness but also the implementation of robust security protocols to secure their digital environments.