Cybersecurity professionals are raising urgent concerns about the escalating threat of zero-day attacks, sophisticated cyber assaults that exploit previously unknown vulnerabilities in computer systems and networks. During discussions on April 3, 2023, industry experts highlighted how these attacks represent one of the most dangerous forms of cyber threats facing organizations today.
Zero-day attacks derive their name from a critical timing vulnerability: they target security flaws that have never been discovered or publicly reported, meaning there are zero days of advance warning or preparation time available to potential victims. This lack of awareness leaves organizations completely exposed, with no existing patches or defenses in place when attackers strike.
"These attacks can be particularly dangerous because they can be launched without the knowledge of the affected parties and can be very difficult to detect and prevent," explained an industry analyst familiar with the threat landscape.
"These attacks can be particularly dangerous because they can be launched without the knowledge of the affected parties and can be very difficult to detect and prevent,"

The stealth nature of zero-day attacks makes them exceptionally valuable to cybercriminals, who leverage these undiscovered vulnerabilities to steal sensitive data, disrupt critical services, or deploy malicious software for espionage and sabotage operations. The attacks can go completely unnoticed by victims, sometimes for months or even years, allowing perpetrators to maintain persistent access to compromised systems.
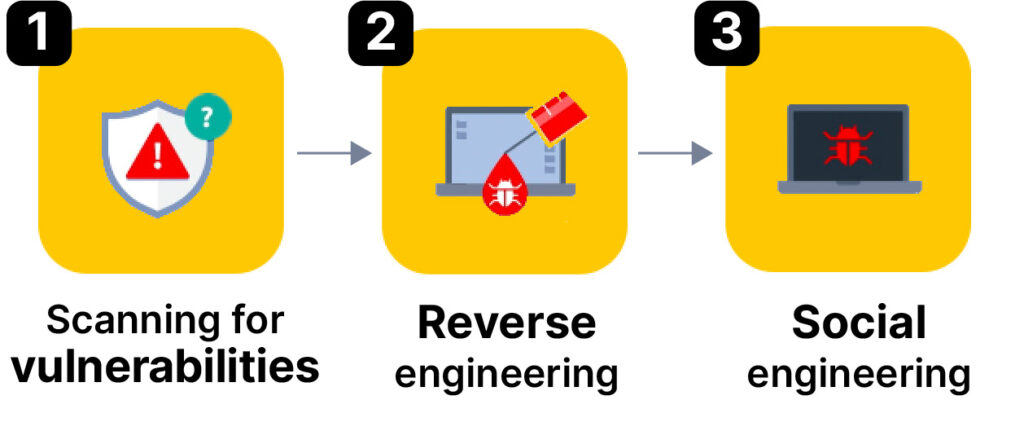
Understanding how these attacks unfold is crucial for organizations seeking to protect themselves. Cybercriminals employ several sophisticated methods to uncover exploitable vulnerabilities. Social engineering remains one of the most prevalent tactics, with phishing campaigns designed to trick individuals into revealing confidential information or inadvertently installing malware on corporate networks.
Reverse engineering presents another significant threat vector, where skilled hackers methodically dissect software and hardware components to identify exploitable weaknesses that developers never anticipated. Additionally, cybercriminals use specialized vulnerability scanning tools to systematically probe systems and networks, searching for security flaws that can be weaponized.
Team Dynamics
Once hackers identify a zero-day vulnerability, they move quickly to exploit it before security teams can discover and patch the flaw. This creates a dangerous race against time, where organizations often find themselves responding to attacks rather than preventing them.

"It can become a race against the clock to patch vulnerabilities after they've been taken advantage of," noted a cybersecurity vendor representative, emphasizing the reactive nature of many current security approaches.
"It can become a race against the clock to patch vulnerabilities after they've been taken advantage of,"
The challenge of detecting zero-day attacks has pushed security experts to develop more sophisticated defense strategies. Traditional signature-based detection methods, which rely on identifying known threat patterns, prove inadequate against attacks exploiting previously unknown vulnerabilities.
Security professionals now recommend implementing hybrid detection methods that combine multiple defensive approaches. This strategy typically involves pairing signature-based detection techniques with behavior-based monitoring systems, creating a more comprehensive security framework capable of identifying suspicious activities even when specific threat signatures aren't yet known.
Behavior-based monitoring has emerged as a particularly promising approach, allowing organizations to track software and system behavior for irregularities that might signal a zero-day exploit in progress. While this method can produce false positives, it offers the advantage of detecting previously unknown threats by focusing on abnormal system behavior rather than specific malware signatures.
Signature-based detection, while limited in its ability to catch new threats, remains valuable for identifying known zero-day exploits that have been documented and analyzed by security researchers. The key lies in combining these approaches to create multiple layers of defense.
Experts emphasize that organizations must move beyond reactive security measures and adopt proactive strategies to reduce their vulnerability to zero-day attacks. Regular software updates remain fundamental to cybersecurity hygiene, as they ensure that known vulnerabilities are patched as quickly as possible.
"Vigilance is key—we must detect and respond to any unusual activity swiftly," emphasized a cybersecurity executive, highlighting the critical importance of maintaining constant awareness of potential threats.
"Vigilance is key—we must detect and respond to any unusual activity swiftly,"
Implementing robust security protocols forms another cornerstone of effective zero-day defense. This includes establishing comprehensive monitoring systems, maintaining detailed logs of system activities, and ensuring rapid incident response capabilities.
Impact and Legacy
The growing sophistication of zero-day attacks reflects the evolving nature of cyber threats in an increasingly digital world. As organizations become more dependent on technology for critical operations, the potential impact of successful zero-day attacks continues to expand. Data breaches, service disruptions, and system compromises can have devastating consequences for businesses, government agencies, and individuals alike.
Security experts stress that maintaining system integrity in this hostile digital landscape requires a multi-faceted approach combining advanced detection technologies, regular security updates, comprehensive monitoring, and well-trained personnel capable of responding quickly to emerging threats. Organizations that fail to implement these protective measures leave themselves vulnerable to attacks that can remain undetected until significant damage has already occurred.