In a significant development in cybersecurity, the CVE-2025-43300 vulnerability has been identified as a zero-day exploit, threatening users of Apple’s Image I/O software. This flaw possesses a CVSS score of 8.8, indicating the severity of the issue, particularly for those who process images using this technology.
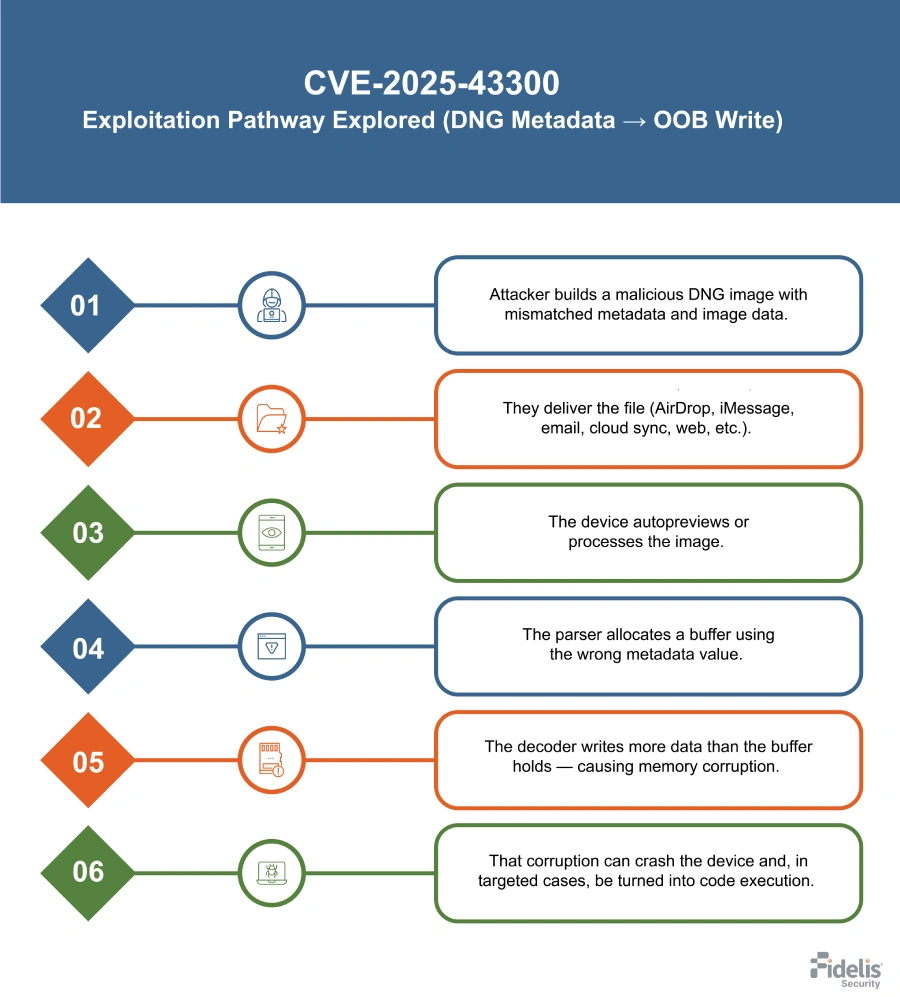
The issue revolves around an out-of-bounds write vulnerability, also referred to as CWE-787. This occurs when a crafted DNG or JPEG-lossless image is processed incorrectly, leading to a buffer overwrite. Such a scenario arises when there is a mismatch between metadata—like TIFF SamplesPerPixel—and the JPEG SOF3 component count. According to analysts, unpatched systems dealing with affected files may experience detrimental effects ranging from memory corruption to crashes, with an alarming potential for arbitrary code execution in targeted attacks.
"Unpatched systems processing these types of files should act immediately to protect themselves from severe security breaches," said a cybersecurity analyst who wishes to remain anonymous. The warning has been echoed by numerous experts, highlighting the immediate impact this vulnerability could have.
"Unpatched systems processing these types of files should act immediately to protect themselves from severe security breaches,"

Apple has not remained idle on this issue. The company has swiftly addressed the vulnerability, rolling out fixes across its platforms, including iOS, iPadOS, and macOS.
"Swift response to known vulnerabilities is crucial in maintaining user safety and trust, and Apple has set an example by providing updates in a timely manner," commented a spokesperson from the cybersecurity community.
"Swift response to known vulnerabilities is crucial in maintaining user safety and trust, and Apple has set an example by providing updates in a timely manner,"

In light of this new exploit, the Cybersecurity and Infrastructure Security Agency (CISA) has taken action by including this CVE in its Known Exploited Vulnerabilities list. This addition alerts organizations and individuals to the pressing need for applying updates as soon as they become available.
Organizations utilizing Apple technologies are strongly urged to take immediate steps to mitigate potential risks. IT departments should employ mobile device management (MDM) tools to enforce updates across corporate devices. Identifying any unpatched devices and promptly applying the necessary updates is vital.
"Using MDM tools can greatly reduce the complexity of managing updates across different devices. It ensures that all users are protected consistently," said a leading cybersecurity expert.
For specific updates, Apple recommends that users upgrade Macs to versions including macOS Sequoia 15.6.1, Sonoma 14.7.8, or Ventura 13.7.8. iPhones and iPads should be simultaneously updated to iOS/iPadOS 18.6.2 to stay protected from the vulnerabilities posed by CVE-2025-43300.
"Ignoring updates can lead to disastrous outcomes, and we cannot stress enough the importance of being proactive in cybersecurity," reiterated the cybersecurity analyst. The reality is that while organizations move toward greater digital capabilities, they must also fortify their defenses against emerging threats.
"Ignoring updates can lead to disastrous outcomes, and we cannot stress enough the importance of being proactive in cybersecurity,"
The ongoing landscape of cybersecurity threats emphasizes the importance of vigilance. As vulnerabilities like CVE-2025-43300 surface, timely updates and user education become indispensable tools in maintaining a secure digital environment. The current exploit serves as a critical reminder for organizations to remain alert and responsive to potential threats, ensuring their systems are shielded against malware and attacks in the ever-evolving landscape of cybersecurity.